Cybersecurity academics have discovered a continuous and ambitious program that aims thousands of Docker servers every day with a Bitcoin (BTC) mining hardware.
Cybersecurity academics have discovered a continuous and ambitious program that aims thousands of Docker servers every day with a Bitcoin (BTC) mining hardware.
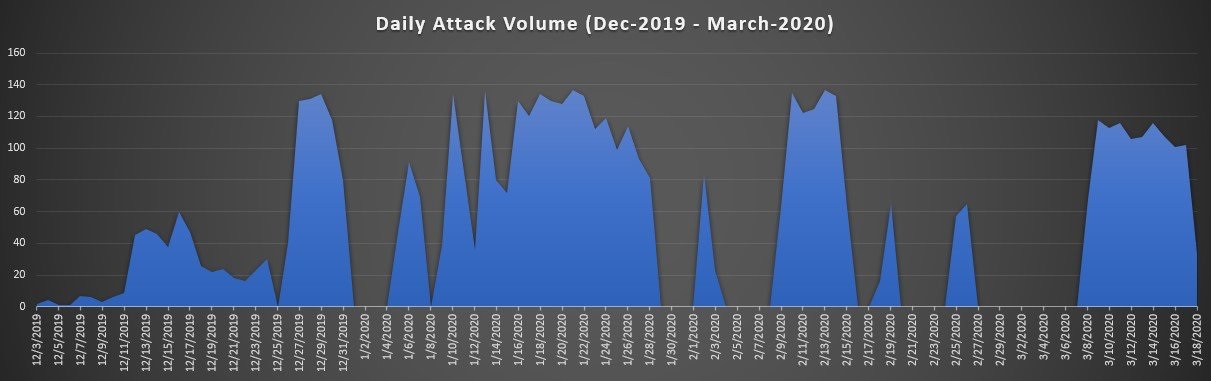
In a document released on April 3, Aqua Security published a word of caution about the attack, which has supposedly “been going on for months, with thousands of attempts taking place nearly on a daily basis.”
The researchers have cautioned:
“These are the highest numbers we’ve seen in some time, far exceeding what we have witnessed to date.”
Such leeway and aspirations signal that the illegal Bitcoin mining program is implausable to be “an improvised endeavor,” as the players involved in this may be depending on considerable assets and framework.
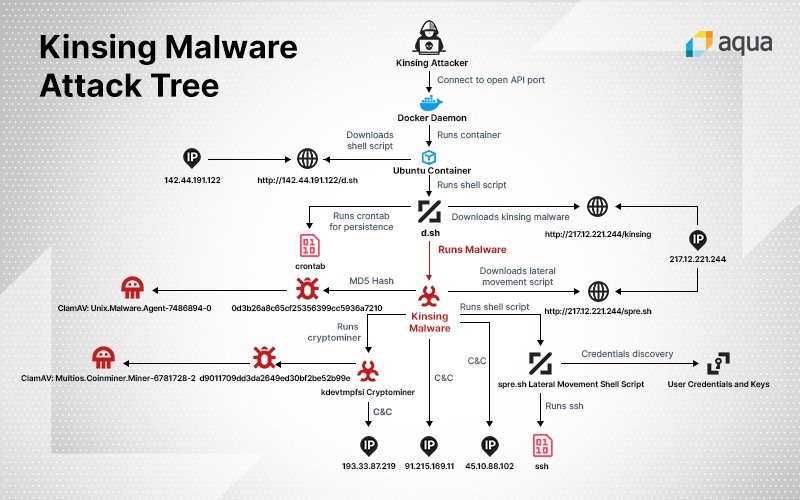
Utilizing its virus analysis toolkit, Aqua Security has discovered the ill-intentioned software as a Golang-based Linux product, referred to as Kinsing. The Trojan spreads by misusing wrong settings in Docker API ports.
The program operates an Ubuntu container, which downloads Kinsing and then intends to propagate the malicious software to other containers and computing devices.
The program’s final objective, accomplished by initially misusing the open port and then conducting a plethora of deception strategy, is to employ a cryptocurrency mining hardware on the jeopardized computing devices, academics stated.
Aqua’s research offers elaborate foresight into the elements of the fraudulent program, which leaps out as a solid illustration of what the company asserts to be “the growing threat to cloud native environments.”
Hackers are raising their game to carry out even more advanced and greedy attacks, researchers have pointed out. As retaliation, enterprise security groups are pooling their resources to build a strong strategy to negate these fresh threats.
Some of their suggestions call for teams to discover all cloud assets and bunch them in a logical framework, assess their validation rules and amend basic safety policies as per a principle of “least privilege.”
Cybersecurity groups should also scrutinize registries to track behavior of users who enroll in an unusual manner, in addition to the installation of cloud safeguard systems to reinforce their plan.
In February, Singapore-powered unicorn company Acronis revealed the outcome of its recent cybersecurity investigation. It disclosed that 86% of IT professionals are worried about cryptojacking, the technical word for the routine of utilizing a system’s handling capacity to mine cryptos without approval or awareness of system owner.