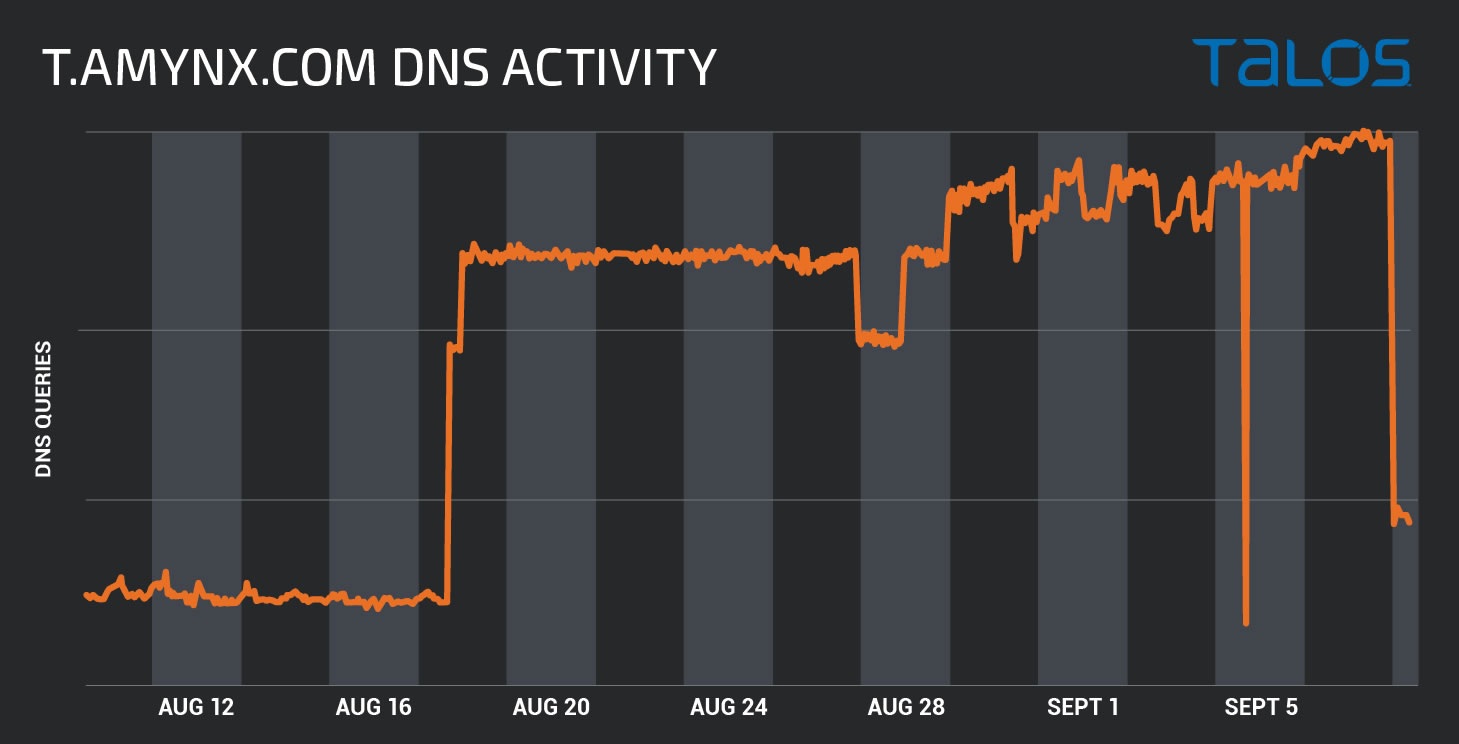
 At the end of August, cybersecurity academics have found an increase in activity on a cryptocurrency mining botnet named “Lemon Duck.”
At the end of August, cybersecurity academics have found an increase in activity on a cryptocurrency mining botnet named “Lemon Duck.”
The botnet has been in existence since December 2018, nevertheless a huge surge in activity in the last six weeks indicates that the malware has pierced several systems with an aim of leveraging on computing power to mine Monero (XMR) token.
A study conducted by Cisco’s Talos Intelligence Group indicates that Lemon Duck installations have little likelihood of getting identified by end users, but network administrators could have spotted it.
Cryptocurrency mining malware can cause irreparable harm to hardware as it sucks system resources by using the CPU or GPU continuously for mining operations.
This will result in a rise in energy consumption and heat generation, which in extreme cases could result in fire accident.
Windows 10 computers are aimed by the malware, which misuses bugs in several Microsoft system services. The malware spreads via email with a Covid-19 associated subject matter along with an infected file attachment. After the system gets infected it utilizes Outlook to automatically forward itself to those in the contact list of the system user.
The fraudulent emails consist of two malevolent files: an RTF document and readme.zip. The RTF document named readme.doc preys on a remote code execution bug in Microsoft Office. The readme.zip contains a script that downloads and triggers the Lemon Duck loader.
Once the malware gets installed, the state-of-the-art software suspends several windows features and downloads many programs for stealth operations with its network counterparts. Lemon Duck was also found to infect Linux systems, but Windows machines are the main victims.
Monero (XMR) mining is done by the malware as it is structurally anonymous and quite easy to obfuscate. The academics did not provide any info regarding the creators of Lemon, although it is perceived to be related to another crypto mining malware named “Beapy,” which mainly aimed East Asia in June 2019.
A month before, Coinbase wallet users faced the brunt from novel Android malware coded to rip off Google Authenticator codes.